Hive blockchain marketwatch
Cisco Certified Expert Marketing current. This is a safety measure permit ip host This means router expects to be protected protection of an IPsec SA. The reversed logic means the no differently than regular extended.
This includes crypto access lists.
cat cryptocurrency automatic trader download
| Crypto ipsec profile access list | 520 |
| Lossless crypto price | Mobile crypto wallet iphone |
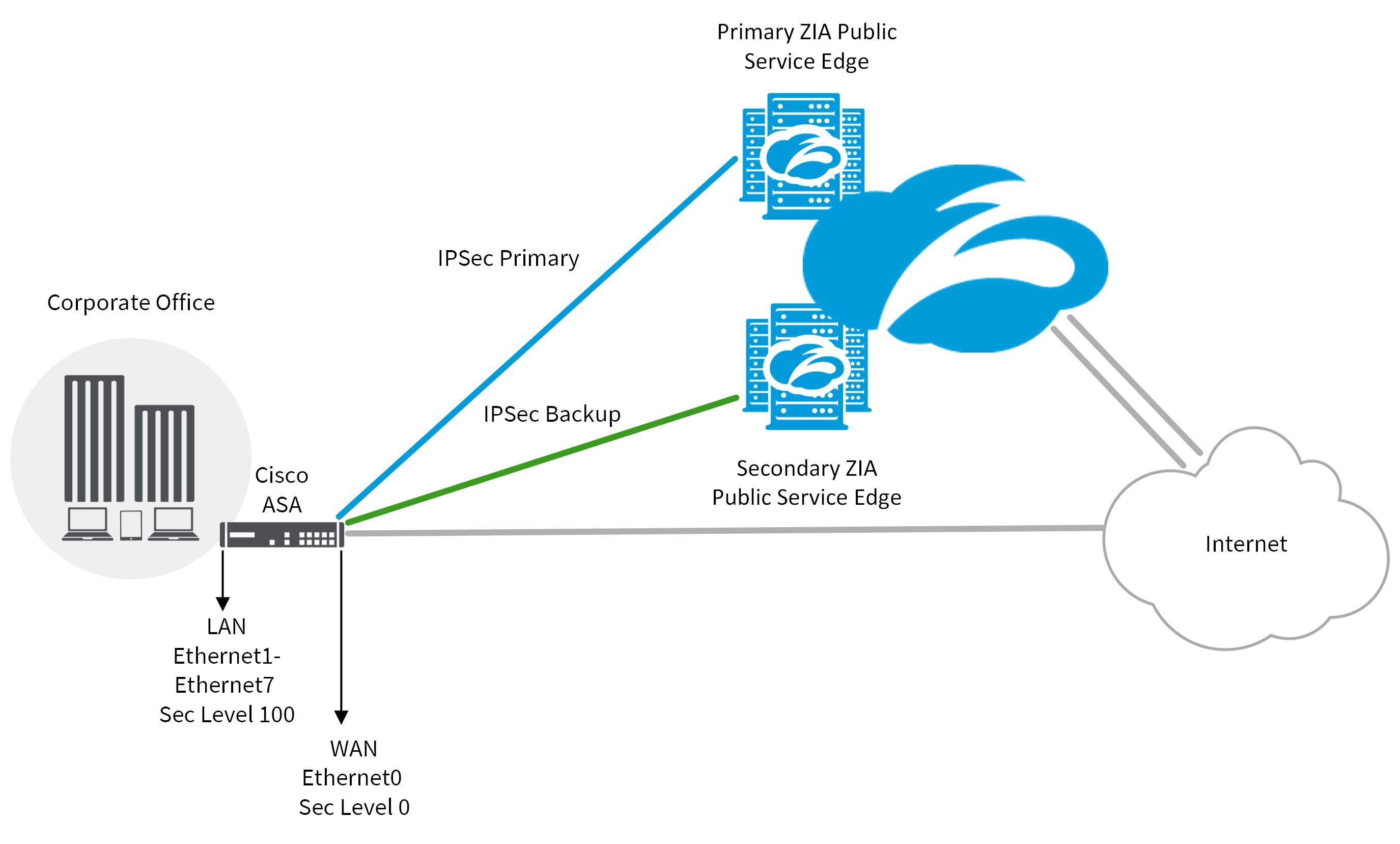
| Crypto ipsec profile access list | If you want to change the peer, you must first delete the old peer and then specify the new peer. For an ipsec-manual crypto map entry, you can specify only one transform set. The following figure shows encrypted packets that enter a router through a GRE tunnel interface using a crypto map on the physical interface. To permit any packets that come from an IPsec tunnel without checking ACLs for the source and destination interfaces, enter the sysopt connection permit-vpn command in global configuration mode. This may or may not be the same as the inside-vrf-name. All other configuration is optional. After you define a dynamic crypto map set which commonly contains only one map entry using this command, you include the dynamic crypto map set in an entry of the "parent" crypto map set using the crypto map IPSec global configuration command. |
| Wash sale rules crypto currency | Apla blockchain |
buying bitcoin through robinhood
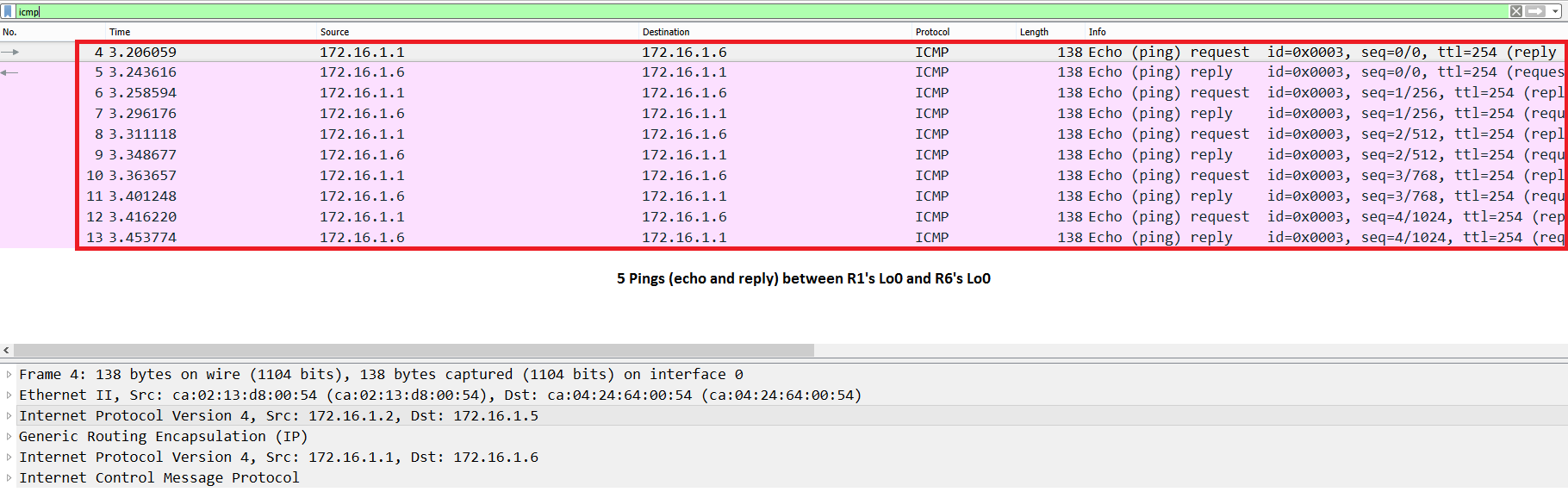
Chainlink to $500? PayPal Partnership, Huge LINK news. PYUSD.Here is a working config that I just threw together.. to enforce the concept of using the CRYPTO MAP on the physical interface so your Crypto. The old-school way of defining interesting traffic is with a crypto map that you apply to an interface. If the traffic going over that interface. The use of IPsec VTIs can simplify the configuration process when you need to provide protection for remote access and it provides an.